Hello, Everyone,
This post will explain You some more Azure AD premium features which includes:
Let's start with explanation!
Configure MFA for Azure AD Users:
Click on Azure Active Directory Premium:
Click on Assign Users to Provide Licence to the Users:
Select Users You want to assign and Click on Assign:
Done with licence assigned for MFA to users (Note: Here I have selected only Azure AD Users, not on-premises users):
After that, Go back to Azure Active Directory Premium Page and Click on Enable directory feature:
It will redirect You to Configure Tab, Click on Manage service settings:
You will notice that the users You had assigned licence are still disabled to use MFA feature so You have to select those users and Click on Enable:
Click on Enable multi-factor auth:
You can configure more settings as per your requirements by selecting User and clicking on Enforce and Manage User settings.
Testing for MFA for Azure AD Users:
Login Here with Azure AD User (User with MFA feature enabled).
It will prompt user to set up additional information for security verification:
Provide country code and number, choose option and click on Contact me:
You will receive a verification code from Microsoft, Enter verification code and Click Next:
Click Done:
Again Login Here with above user:
Once You click sign-in, A verification code will be sent to Your mobile. Once You enter that code then only You will be able to login Your account (This is the only additional security layer enabled called MFA):
For first time login, A message will be prompt to verify your information so click on Verify now:
Click on Verify:
Click on either option:
Enter verification code and Click Verify:
Click Finish:
Done with MFA in the cloud:
This post will explain You some more Azure AD premium features which includes:
- Multi-factor Authentication
- Other Features like Group Writeback, Prevent accidental deletes, etc.
To view Part 1, Click Here!
To view Part 2, Click Here!
Let's start with explanation!
Azure Multi-Factor Authentication:
MFA is a additional security layer to Your login portal where You are asked to verify Yourself with either method as below:
- Phone Call
- Text message
- App password on Your smart phone.
These above methods help You to secure Your account with one more security level. After verifying by either of above methods only, You will be able to login to Your account.
MFA is available for Office 365, Azure Administration, EMS Suite and Standalone.
We have two options to use MFA as below:
- MFA in the Cloud
- MFA Server in Your On-Premises environment.
So, Let's Start with first option.
MFA in the Cloud:
Configure MFA for Azure AD Users:
This means You have all Your users on Azure AD and want to provide MFA features to your all or selected users.
For this, You have to open Azure Portal, Click on Azure AD, Click Licence and Click on Activate Trail (If You are using Trail version for Azure AD Premium, This will provide You 100 Licences for Trail version. If You have Licence for Azure AD Premium then You can see Azure AD Premium option):
Click on Tick Mark to activate trail:
Click on Azure Active Directory Premium:
Select Users You want to assign and Click on Assign:
Done with licence assigned for MFA to users (Note: Here I have selected only Azure AD Users, not on-premises users):
After that, Go back to Azure Active Directory Premium Page and Click on Enable directory feature:
It will redirect You to Configure Tab, Click on Manage service settings:
You will notice that the users You had assigned licence are still disabled to use MFA feature so You have to select those users and Click on Enable:
Click on Enable multi-factor auth:
You can configure more settings as per your requirements by selecting User and clicking on Enforce and Manage User settings.
Testing for MFA for Azure AD Users:
Login Here with Azure AD User (User with MFA feature enabled).
It will prompt user to set up additional information for security verification:
Provide country code and number, choose option and click on Contact me:
You will receive a verification code from Microsoft, Enter verification code and Click Next:
Click Done:
Again Login Here with above user:
Once You click sign-in, A verification code will be sent to Your mobile. Once You enter that code then only You will be able to login Your account (This is the only additional security layer enabled called MFA):
For first time login, A message will be prompt to verify your information so click on Verify now:
Click on Verify:
Click on either option:
Enter verification code and Click Verify:
Click Finish:
Done with MFA in the cloud:
MFA Server for On-Premises Environment:
Prerequisites:
- Download Multi-Factor Authentication Server.
- Hardware Requirement:
If firewall is block for outbound on port 443 then below range must be opened:
Installation and Configuration of MFA Server:
Open Azure portal, Click on Your Azure AD, Click on Configure Tab, and Click on Manage Service Setting under Multi-factor authentication:
Click on Go to the portal:
Click on Download:
Click on Download again:
Install downloaded setup file:
Choose location and Click Next:
After installation completed, Click Finish:
New wizard will open, Click Next:
Again Go back to MFA portal and Click on Generate Activation Credentials because this key will be used during installation for authentication purpose:
Credentials will be created:
Enter above credentials and Click Activate:
Provide Group name and Click OK:
Click Yes:
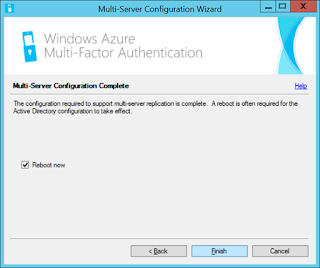
Click next to enable replication:
Choose option as per your environment and Click Next:
Click Next:
Click Finish to reboot:
Post-Configurations:
After reboot, Go to Search and Type Multi-factor authentication Server:
This is MFA Server Console:
Select Users and Click on Import from Active Directory:
Select Users You want to import and Click Import:
Select User and Click Edit:
Now, If You want Users to fill their details and select methods to authentication themselves then leave options by default except marked one (I have provided details like authentication method phone manually instead giving option to user to fill details. If You want to fill details by user itself then You have to send mail to users with Link and PIN as shown below):
Testing for MFA Server on 1 User from on-premises AD:
After enabling, You have to Test if it is prompted for OTP to user. Select User and Click Test:
Enter Password and Click Test:
It Will prompt to enter OTP code, which is sent to User's Mobile, so enter OTP and check if authentication is successful:
Yes, authentication is successful so testing is completed:
Now, when User will login to any on-premises application or cloud application, he has to verify using OTP.
Now, If You want user to fill details itself then Just enable PIN and Click to Email. Enable it and provide SMTP details:
To view or edit the format of Email, Click on Email Content tab:
NOTE: You have many options in MFA Server console to configure as per Your environment as per Your need to Click on options and change settings accordingly.
Once Email is sent to User then a MFA Link will be sent to users to update informations. User have to open link and enter his/her credentials:
He has to provide his details Like mobile number, authentication methods to be used and security questions:
Once done, Your welcome page will be displayed where You can view FAQ, Edit your details like contact number or security questions:
This is all done on MFA Server.
For more details on features, See a small Video Here!
For details explanation of other features in MFA Server console like Users Profile, ADFS, Radius Authentications IIS Authentications etc, Follow below Links:
- User Profile
- ADFS
- Radius Authentication
- IIS Authentication
- Windows Authentication
- LDAP Authentication
- Remote Desktop Gateway and Azure Multi-Factor Authentication Server using RADIUS
- Directory integration between Azure MFA Server and Active Directory
- Getting started the MFA Server Mobile App Web Service
Group Writeback:
This is an optional feature which allow You to writeback Office 365 Group to on-premises AD with Exchange installed.
For more details, See Here!
Other Reference Links:
- Configuring Azure Multi-Factor Authentication
- Azure AD Connect sync: Prevent accidental deletes
- Azure AD Connect sync: Configure Filtering
Happy Reading!!!
If You like my posts then follow me for updates:
Join my Facebook Group for updates on tending technologies/technical references/issues etc:


























































8156D20A63
ReplyDeletetwitter takipçi paketleri
Türk Takipçi Hilesi
Matchpub Jeton Hilesi
Roblox Robux Hilesi
Dragon City Elmas Kodu
Razer Gold Promosyon Kodu
Telegram Üye Hilesi Ücretsiz
Farming Simulator 22 Para Hilesi
white swivel accent chair
E90E27FC6B
ReplyDeleteGörüntülü Seks
Sanal Seks
Webcam Show